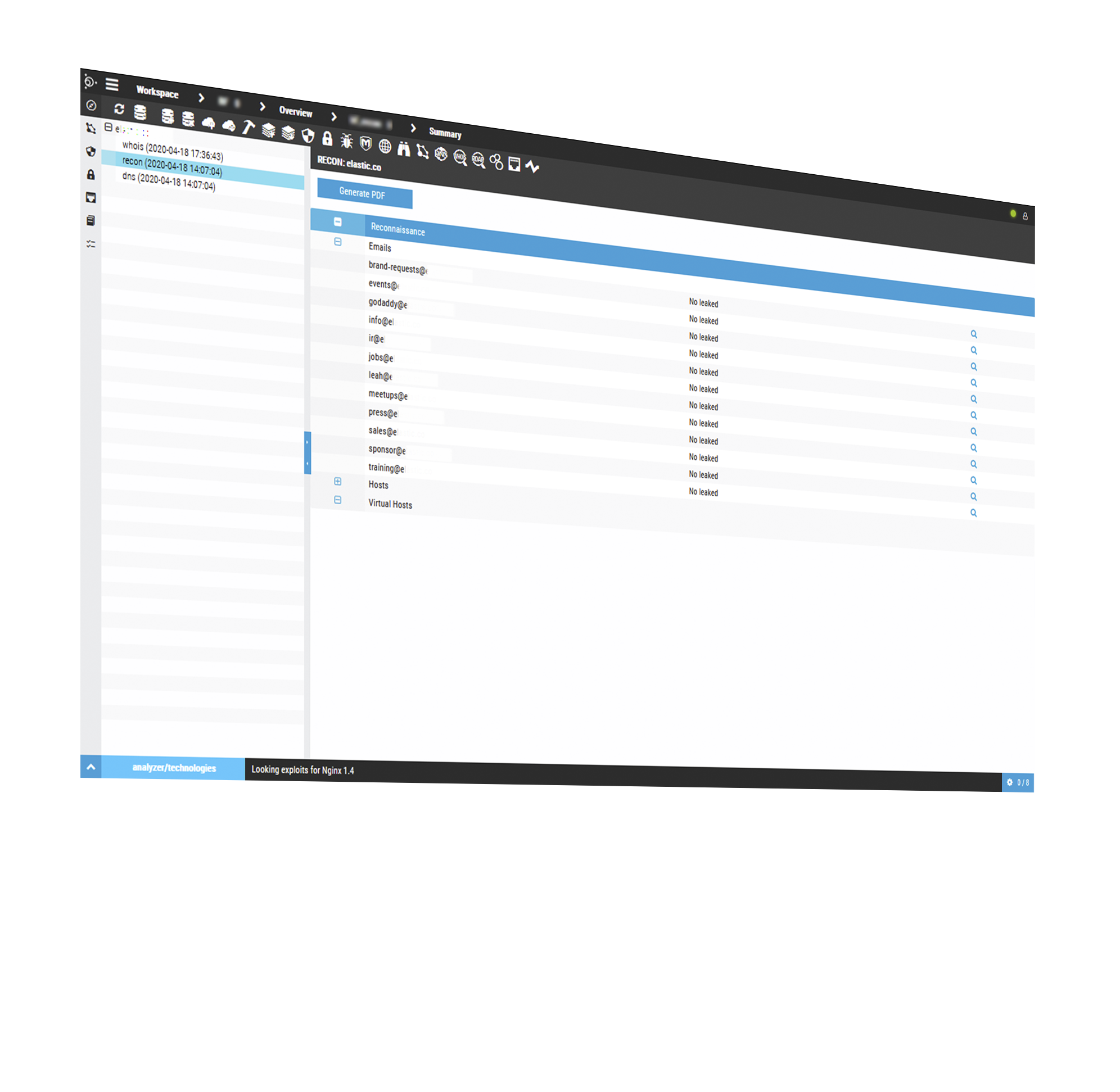
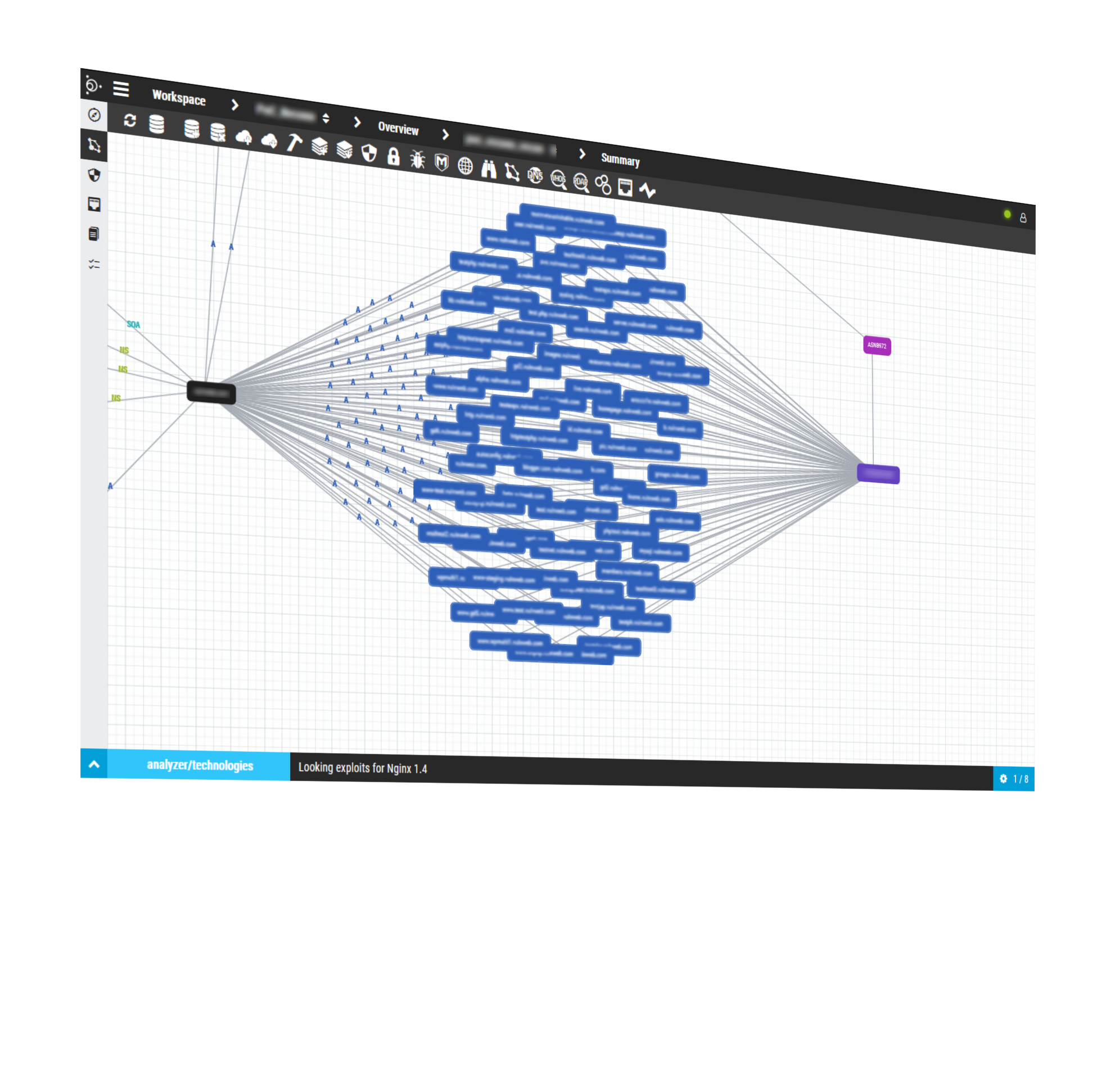
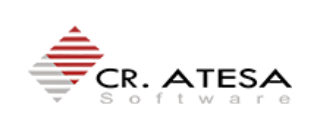
P365 es la única plataforma que realiza un reconocimiento 100% pasivo de activos, puertos, tecnologías web, vulnerabilidades, certificados SSL/TLS, gráficas de DNS, sub dominios, emails y mucho más sin necesidad de escanear o conectarse a los objetivos analizados.
Todo el código fuente está siempre bajo auditoría y revisiones de seguridad, las mejoras y actualizaciones de la plataforma jamás paran y el desarrollo de nuevas funcionalidades está basado en un road map de sugerencias hechas por un equipo de expertos y nuestros propios usuarios.
A diferencia de otras soluciones que tienen múltiples y complejas capas de configuración, en Pentest365 quitamos toda esa complejidad, con el propósito de brindar una experiencia intuitiva y amistosa para el usuario y que este pueda detectar y remediar las vulnerabilidades más rápido y con mayor eficacia.
Nuestra tecnología está orientada a reducir el riesgo tecnológico, bajar el costo operativo y acortar los tiempos de reacción y remediación para optimizar el ROI de tu organización.
Reduce la necesidad de recursos humanos, mejorando la rentabilidad general en la protección de la seguridad y todo desde una consola centralizada que te permita expandir tus capacidades de auditoría sin incrementar tus recursos humanos.
En cuestión de minutos puedes comenzar a escanear toda la Infraestructura de TI de tu organización, sin complicadas y largas instalaciones de agentes en todos los equipos. Tanto en la versión Cloud como Onpremise, la tecnología de P365 no requiere de agentes.
Única plataforma de Análisis de Vulnerabilidades con un módulo de reconocimiento 100% pasivo
Única plataforma de Análisis de Vulnerabilidades con un módulo de reconocimiento 100% pasivo
Única plataforma de Análisis de Vulnerabilidades con un módulo de reconocimiento 100% pasivo
Licencia todo en uno
Obtiene todos los módulos bajo la misma licencia, evite aumentar su inversión de contratos adicionales.
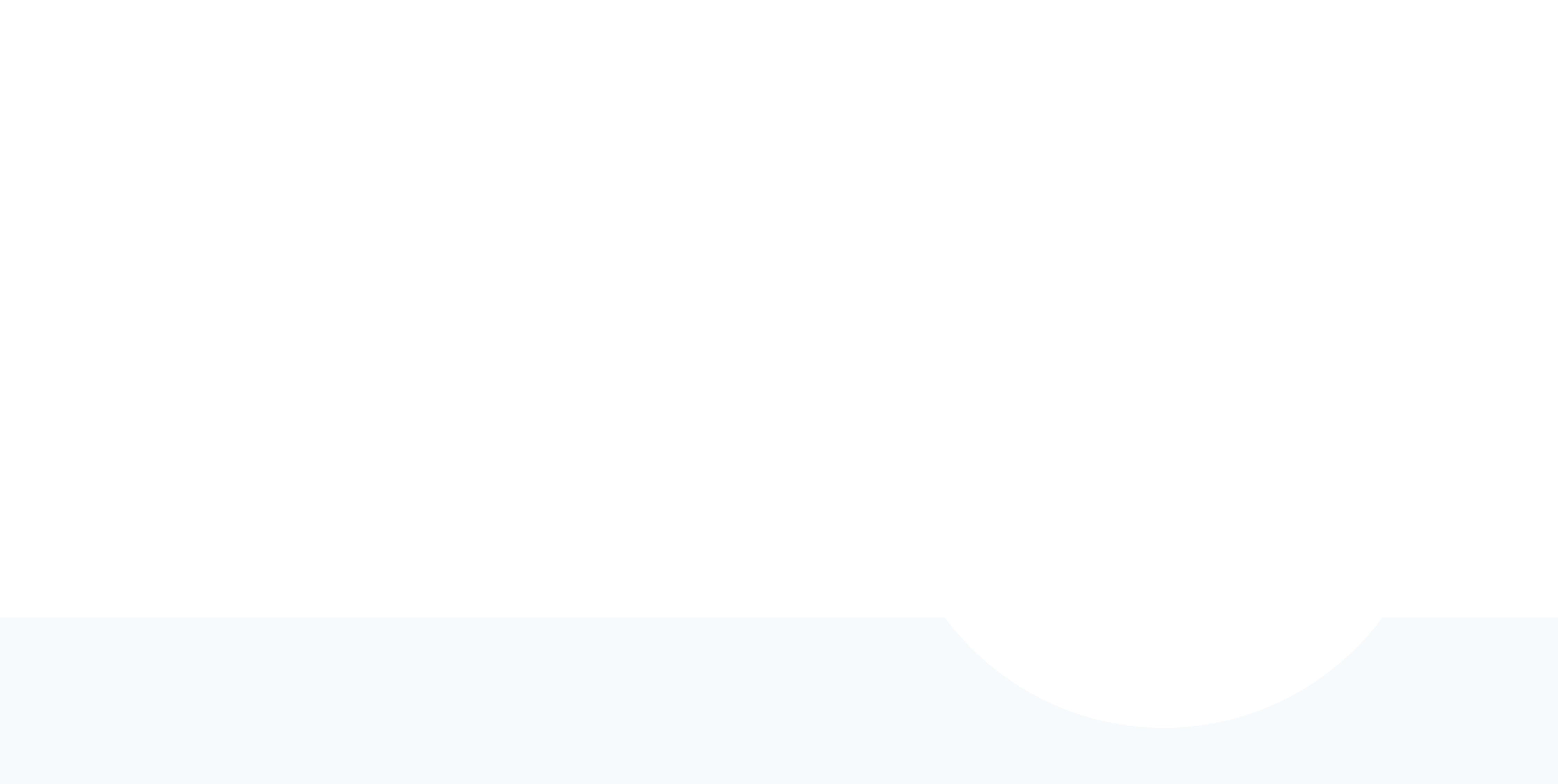
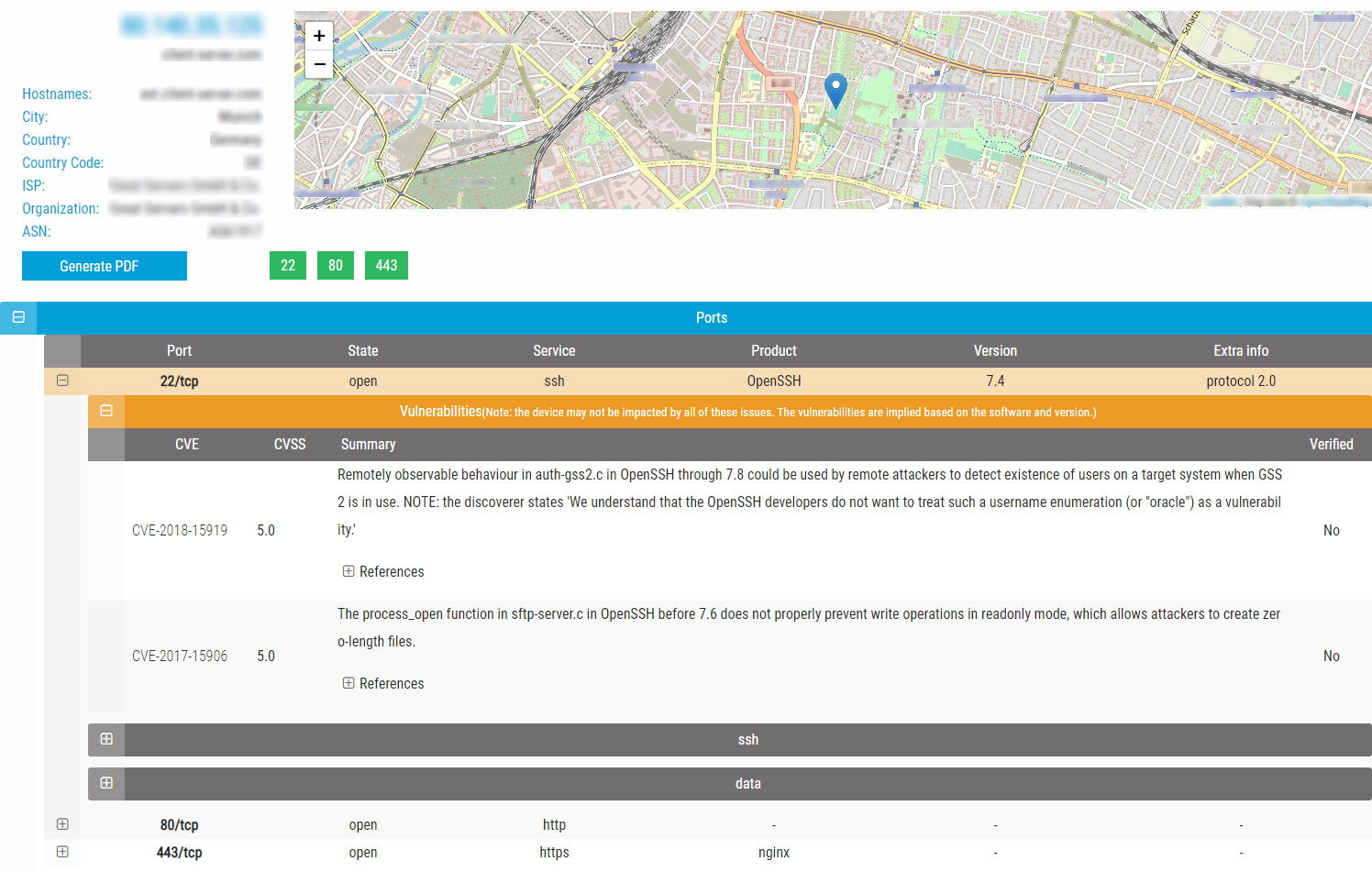
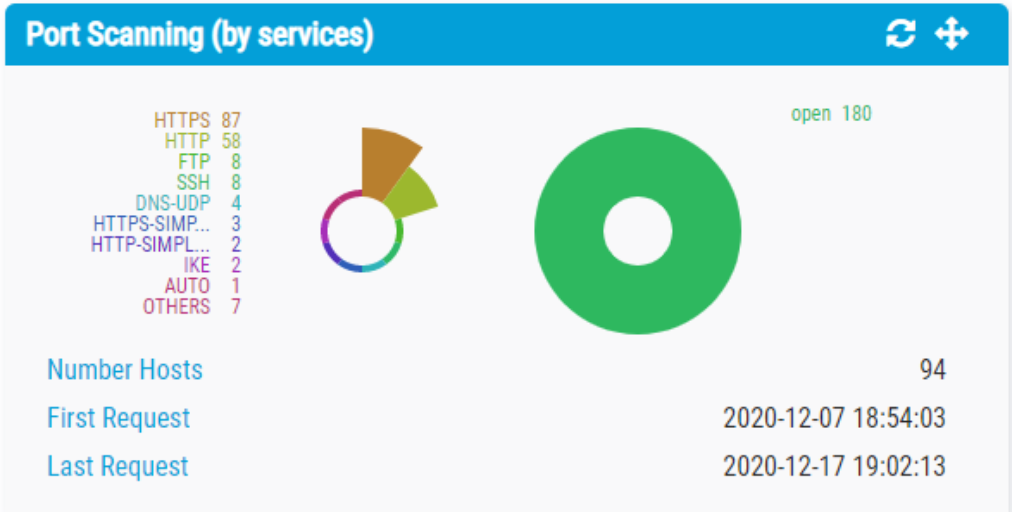
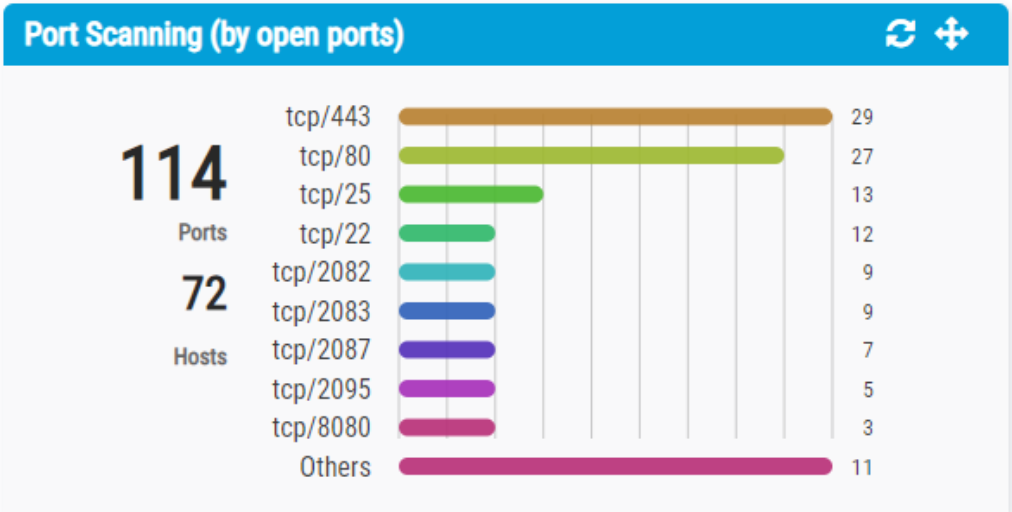
ESCANEO DE PUERTOS
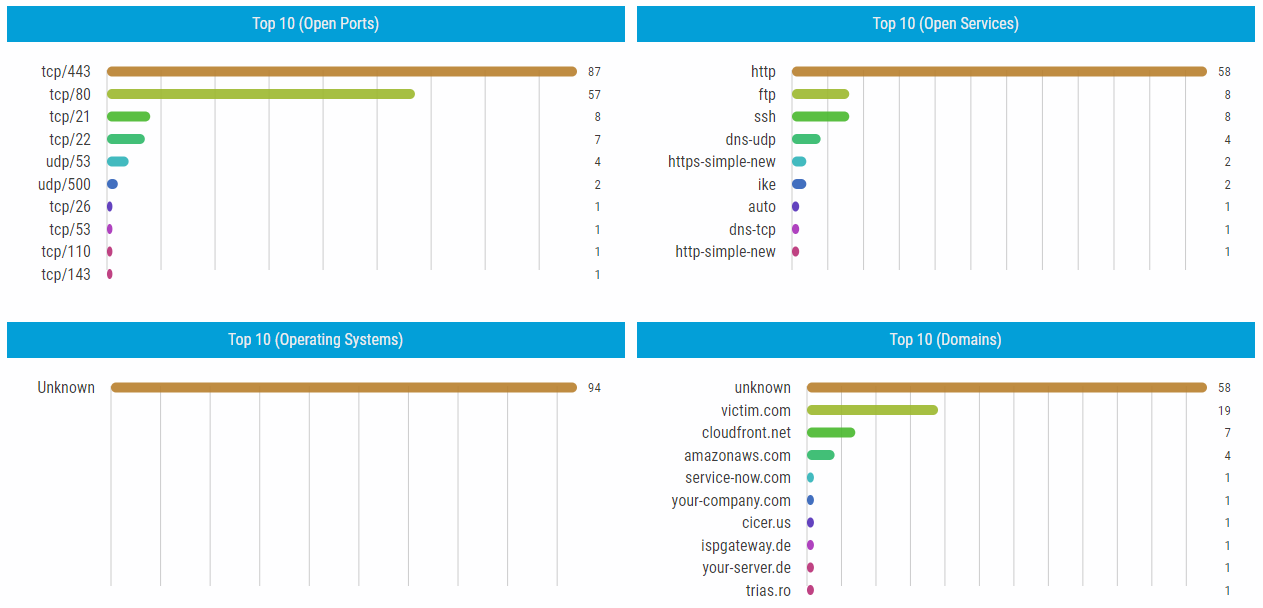
¿Cuentas con una infraestructura expuesta a Internet con cientos o miles de Hosts y necesitas un reporte urgente de tu estado de seguridad?
Pentest365 es tu mejor aliado, facilitándote un completo reporte de Puertos, servicios y Vulnerabilidades de todos tus Hosts en menos de 5 minutos.
Organiza tus escaneos por lista de Hosts, Puertos descubiertos, profile de escaneo, con geolocalización de objetivos y por lista de vulnerabilidades identificadas.
CRAWLING Y MONITOREO DE PORTALES WEB

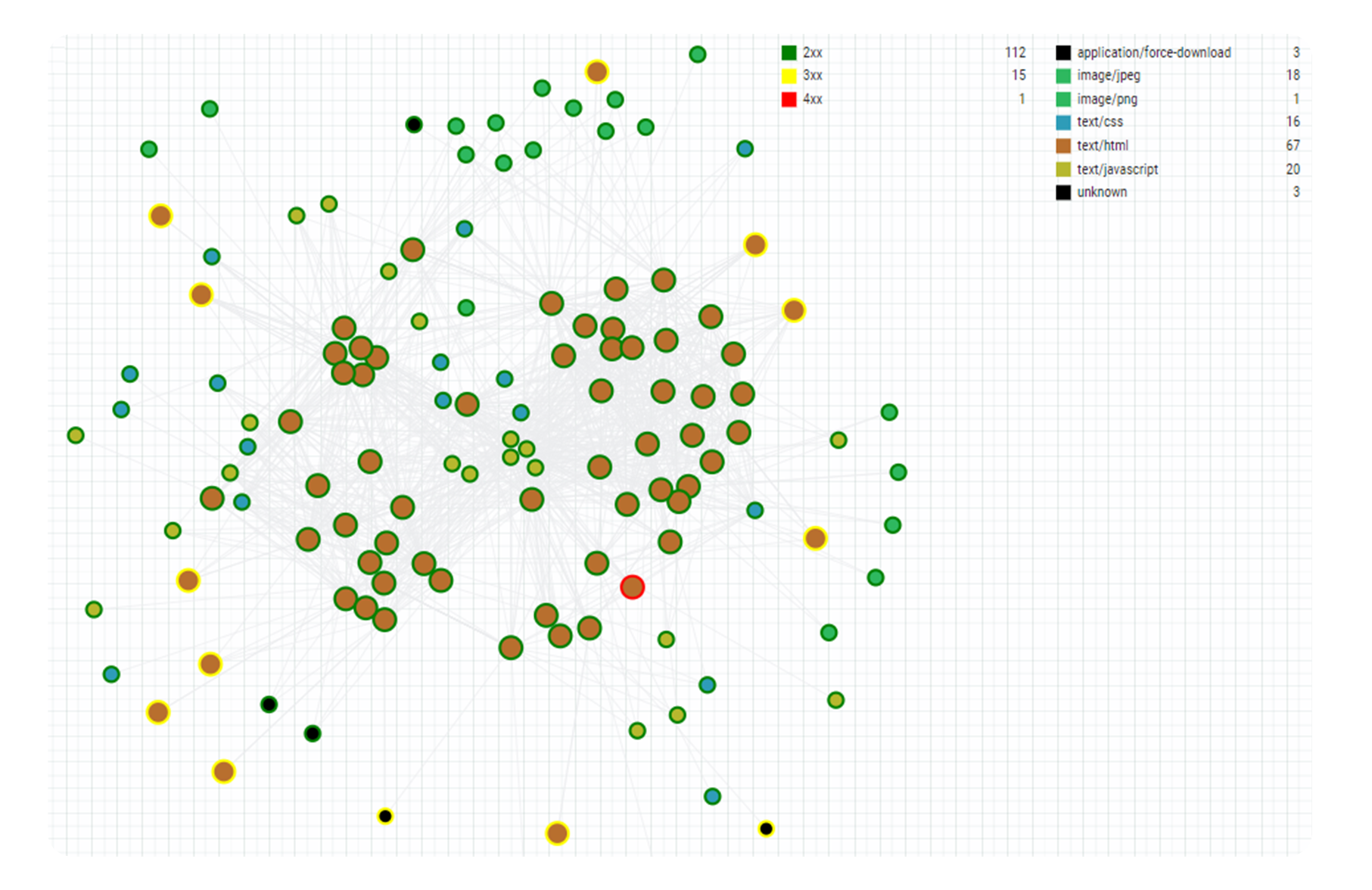
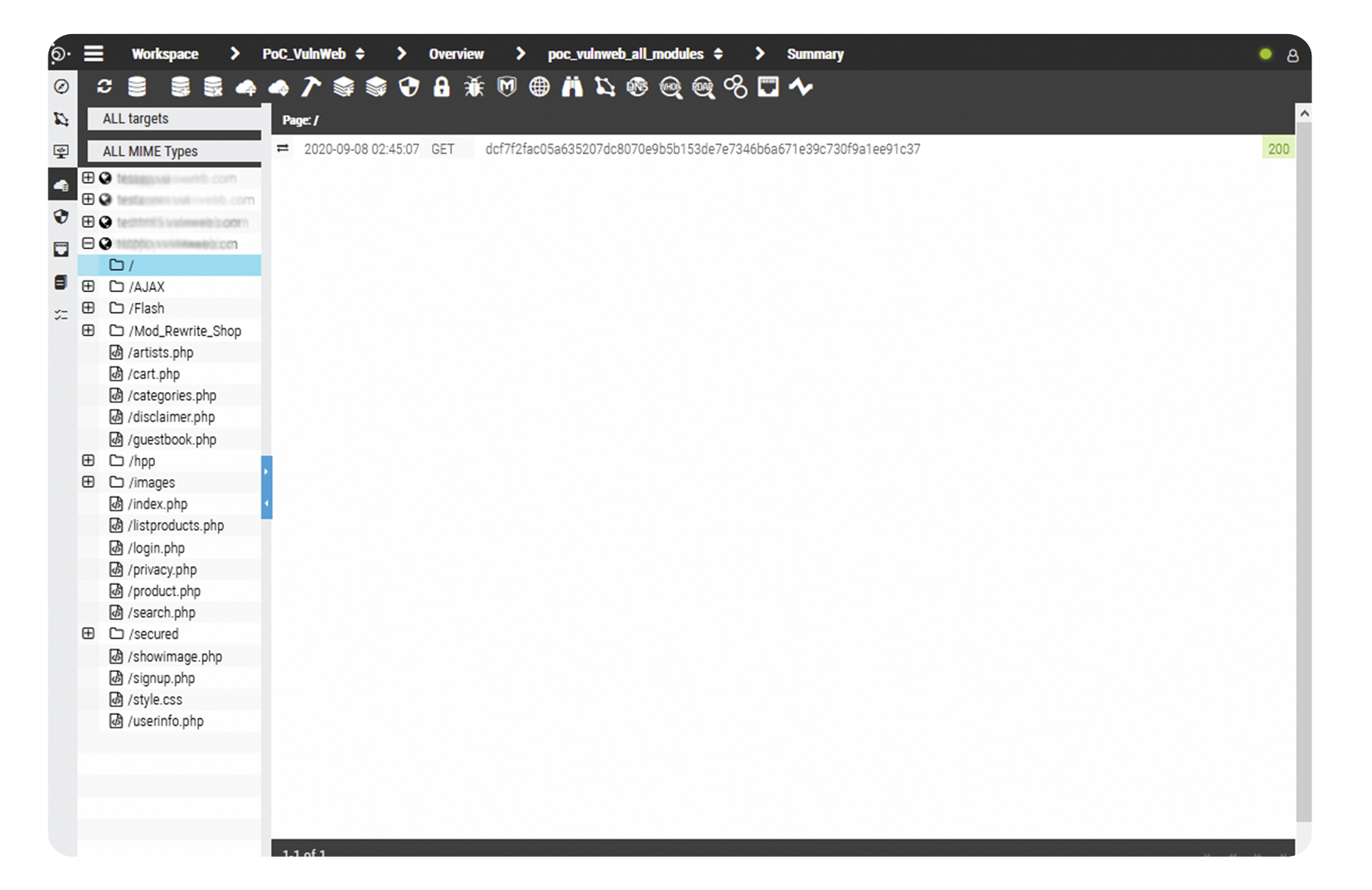
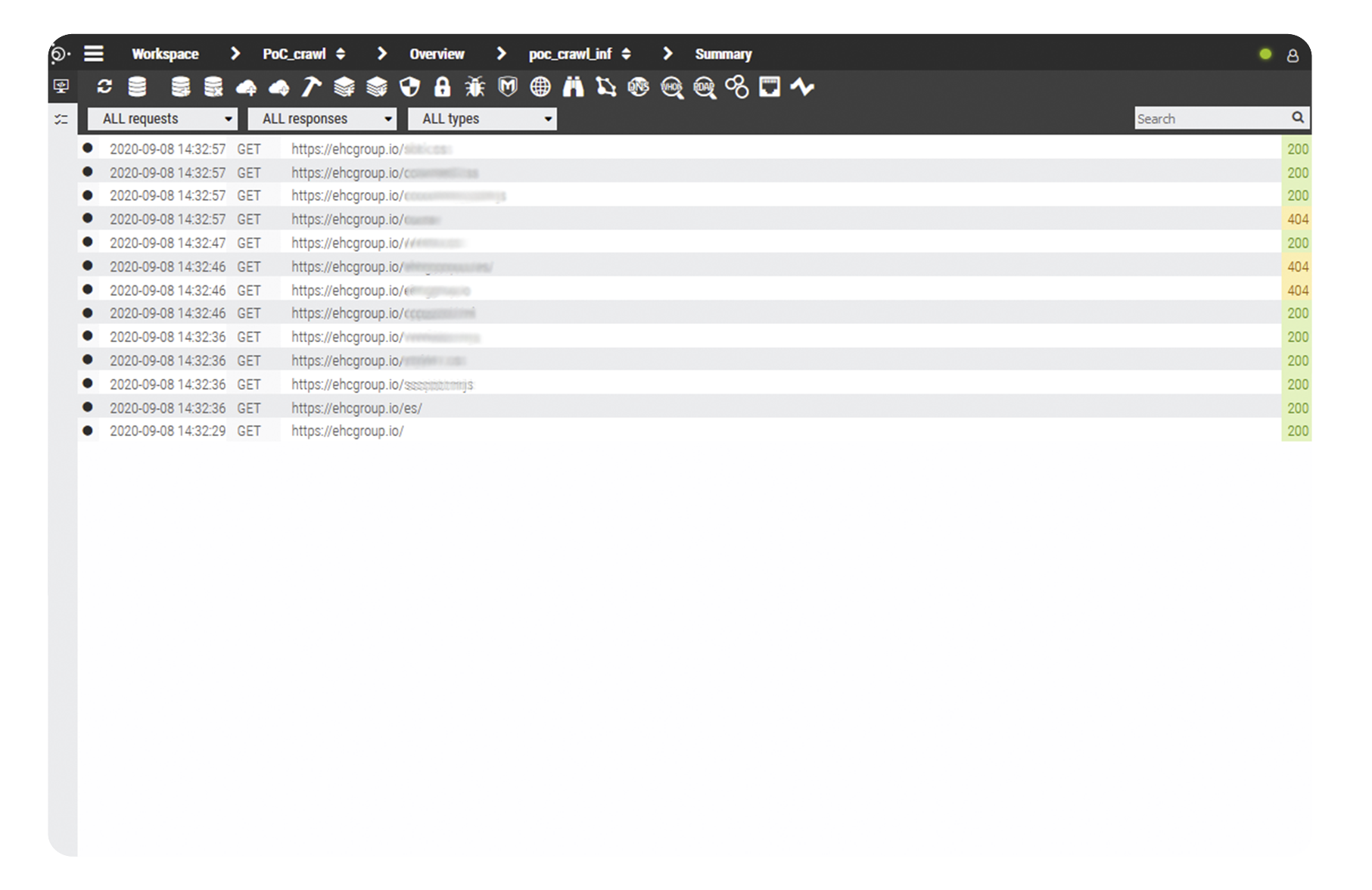
Única e innovadora herramienta de Crawling basada en colores para identificar riesgos en sus portales web de forma rápida y visual.
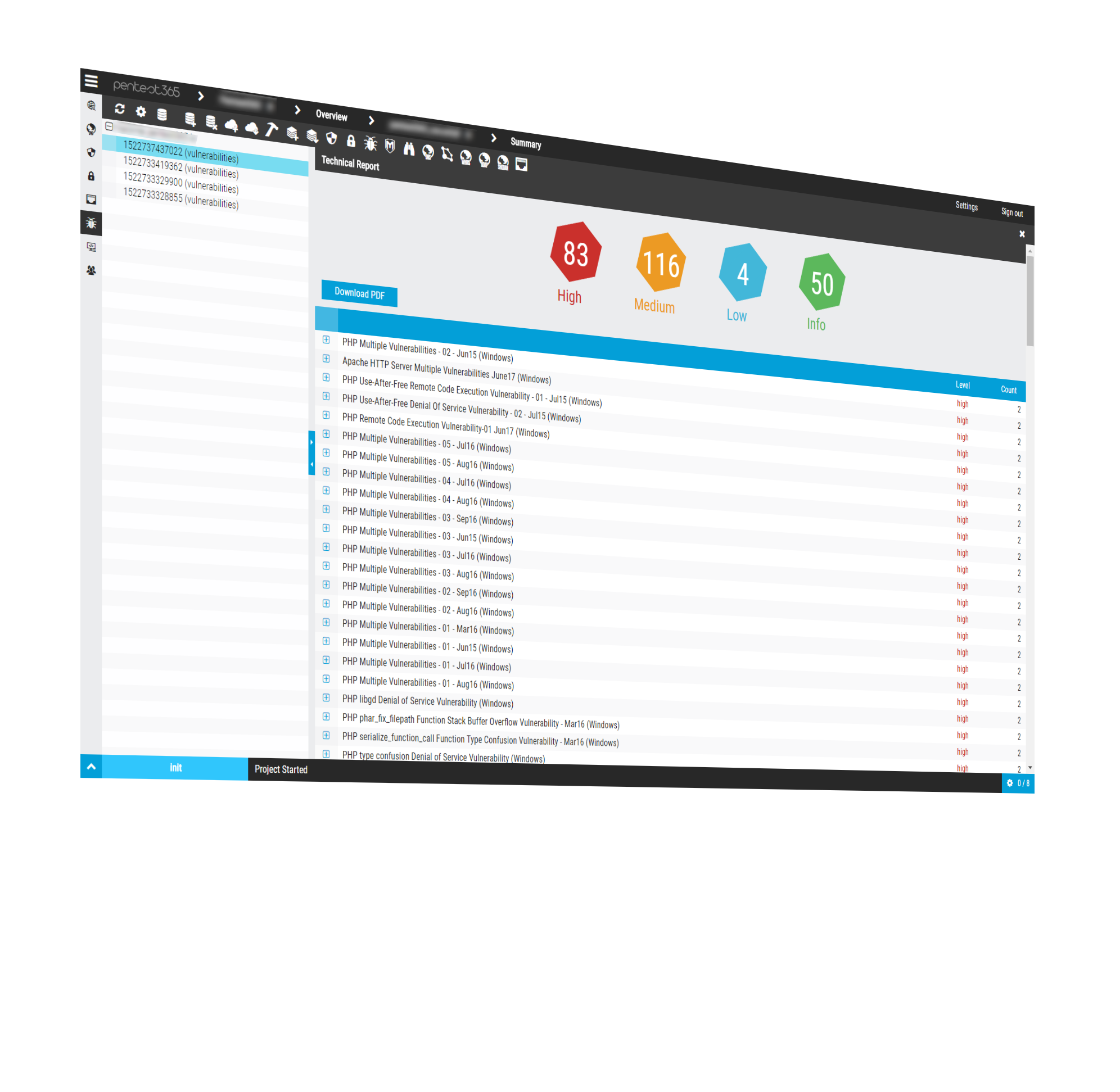
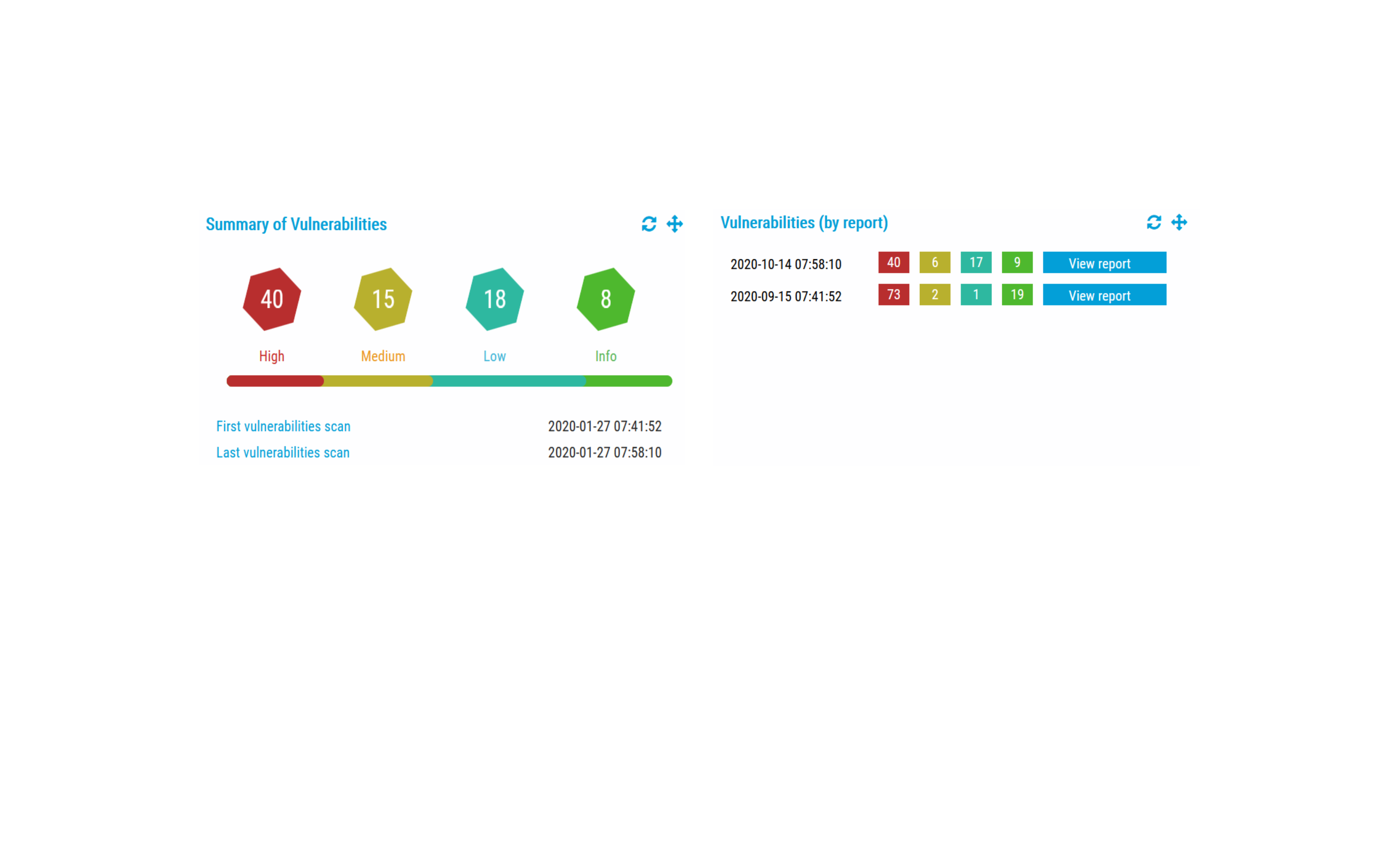
ANÁLISIS DE VULNERABILIDADES PERSISTENTE
Tan fácil como escoger tus objetivos, los tipos de análisis, la periodicidad de los escaneos y obtén tus métricas de riesgo basadas en estándares internacionales y de cumplimiento.
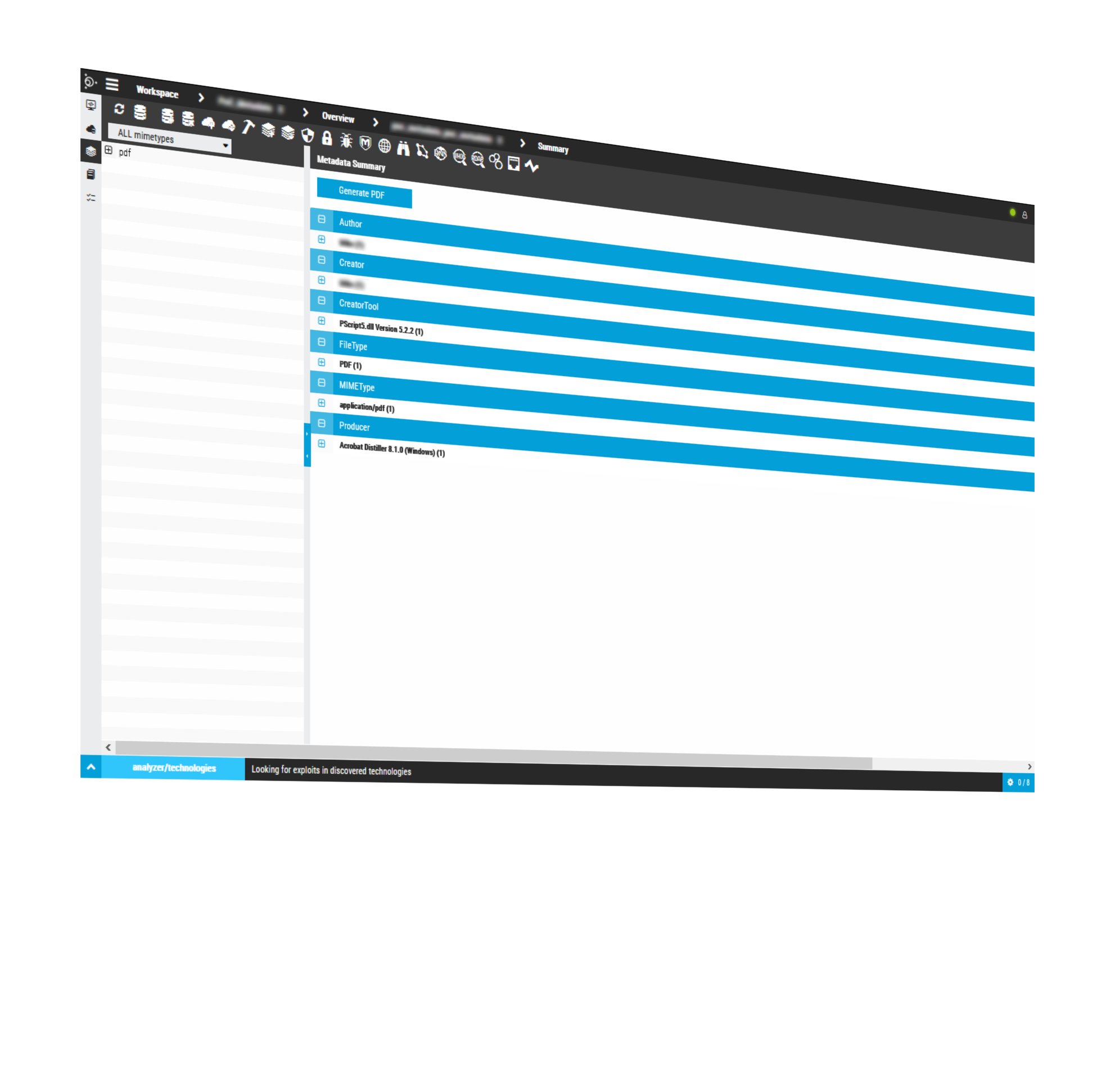
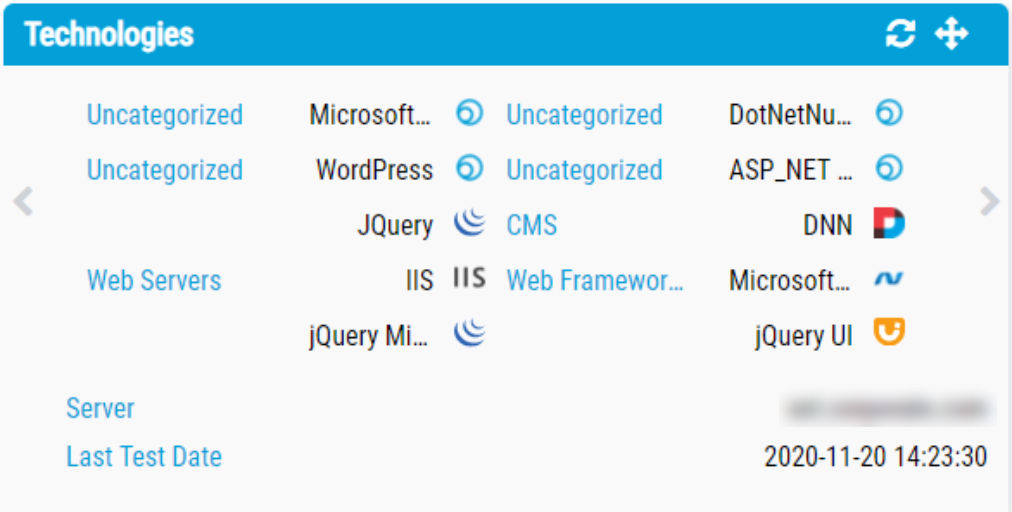
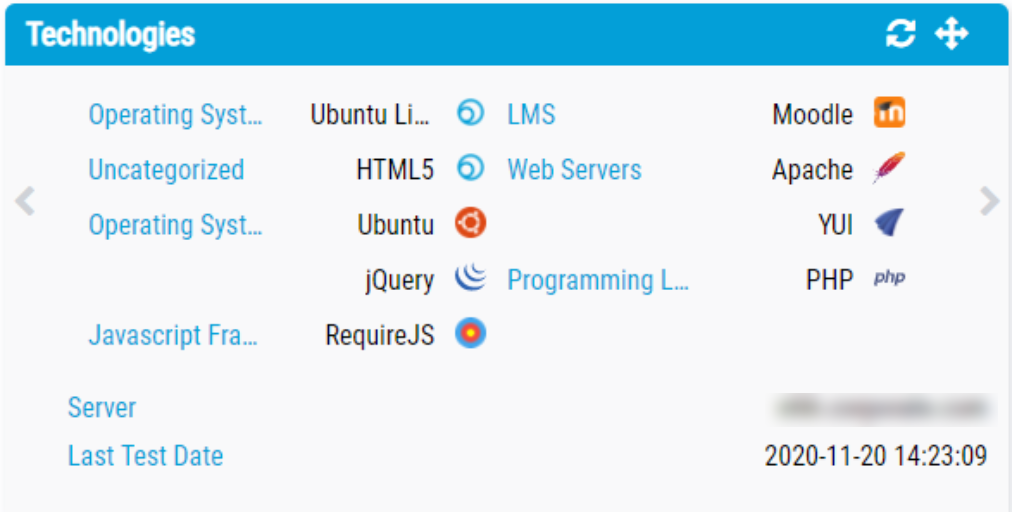
ANÁLISIS DE TECNOLOGÍAS WEB
Descubra de forma pasiva todas las tecnologías web de sus portales y aplicaciones web, identifique la versión en producción y todos los exploits relacionados con esa versión. Podrás revisar o descargarte los exploits en tiempo real.
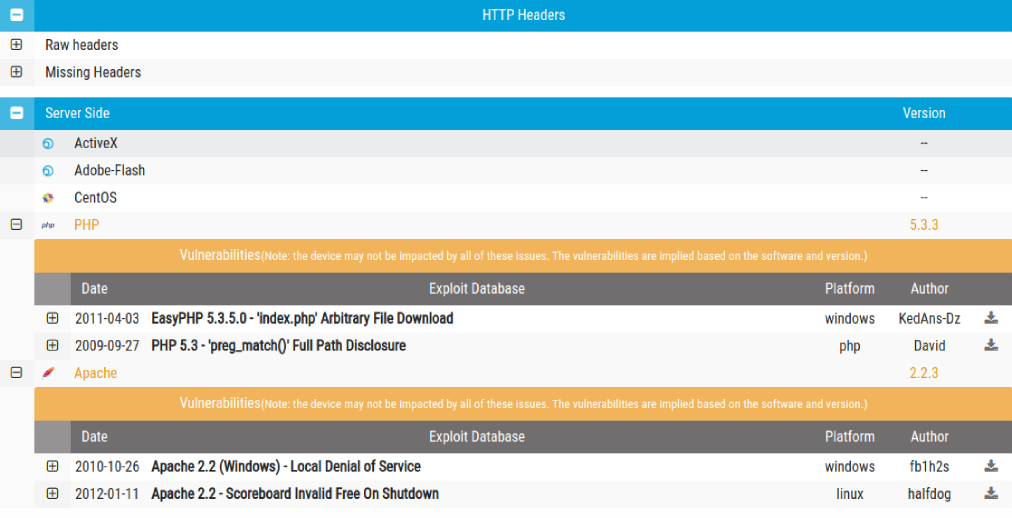
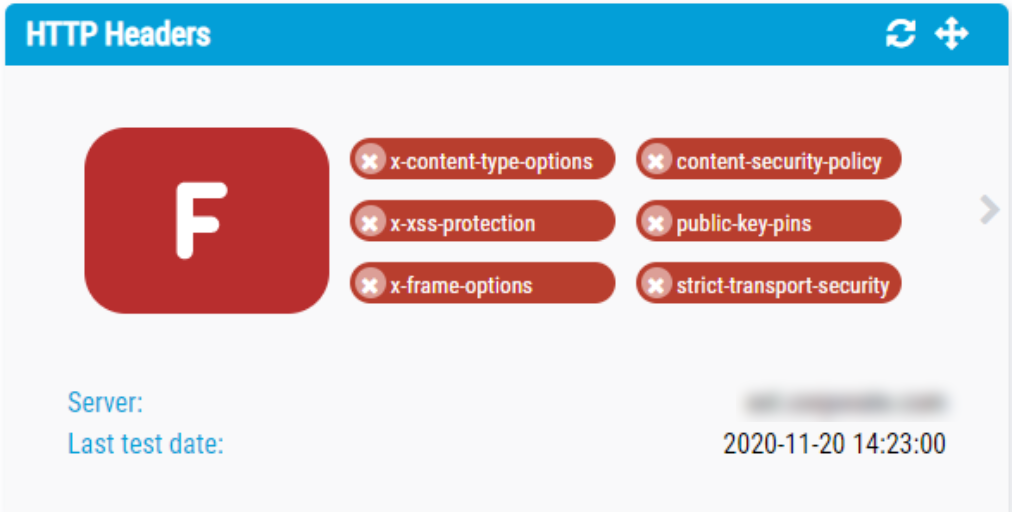
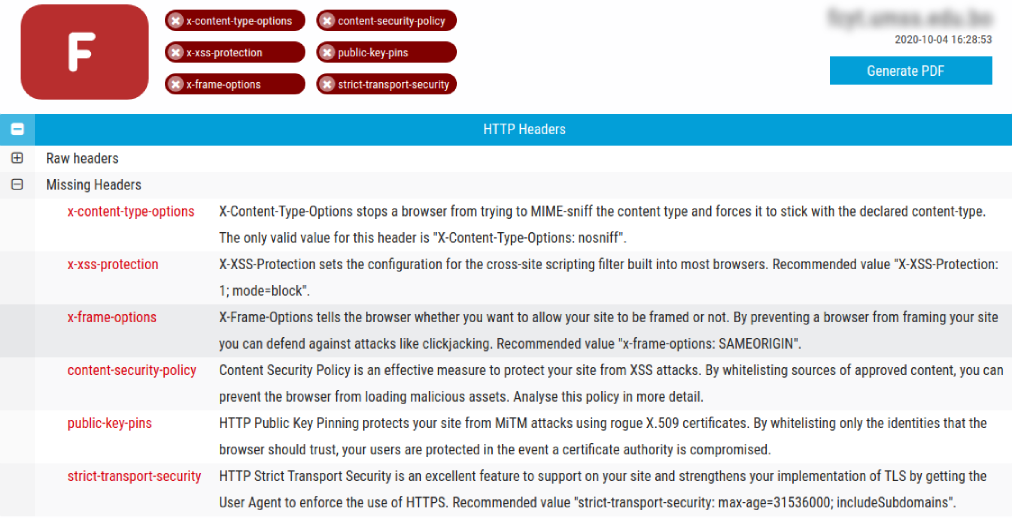
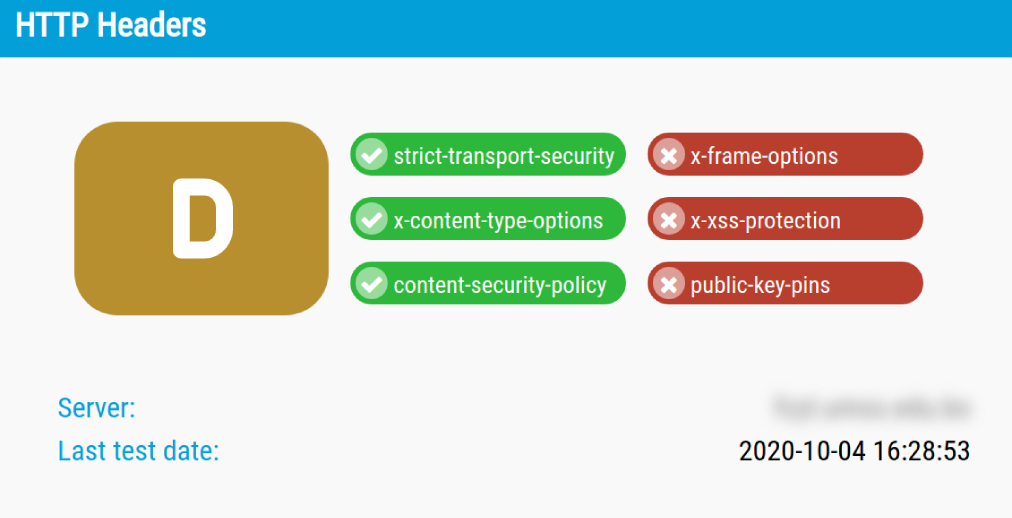
ANÁLISIS DE CABECERAS HTTP/HTTPS
Gran parte de las vulnerabilidades de infraestructura en aplicaciones web están ligadas a vulnerabilidades y fallas de configuración en las Cabeceras HTTP/HTTPS de sus servidores Web. Con Pentest365 usted puede identificar todas estas vulnerabilidades en cuestión de segundos.

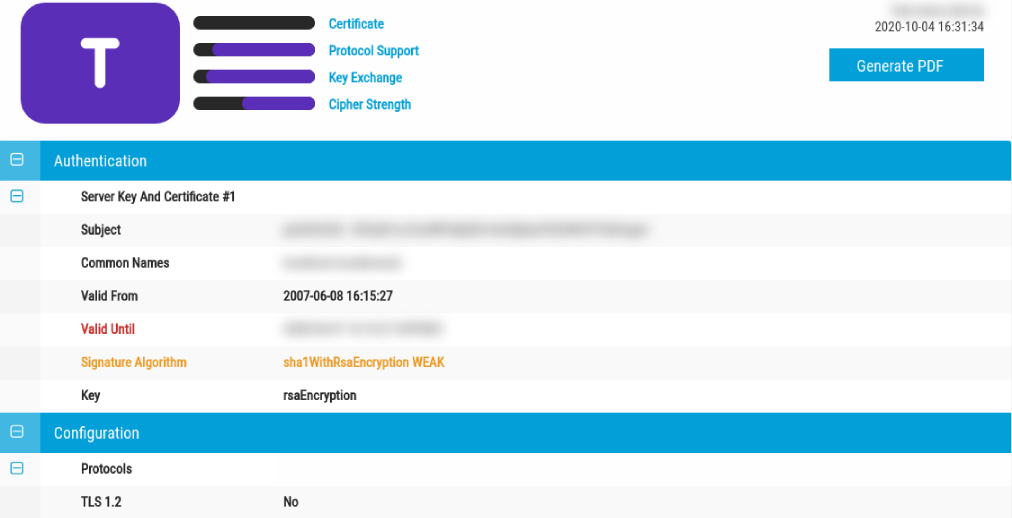
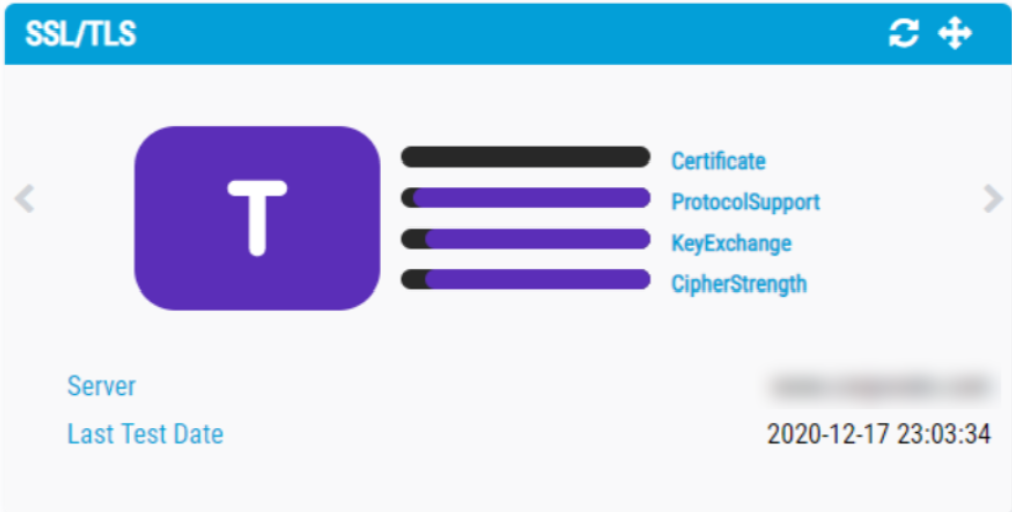
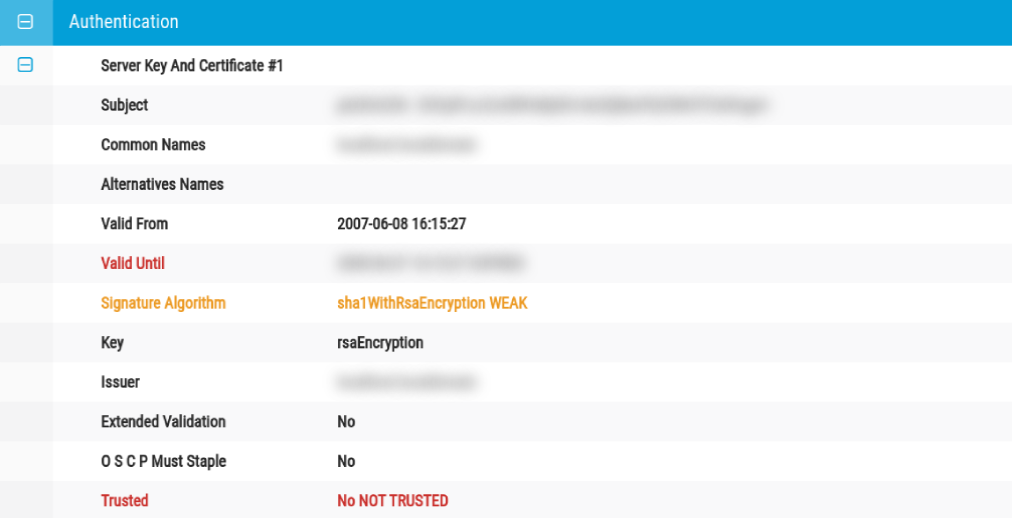
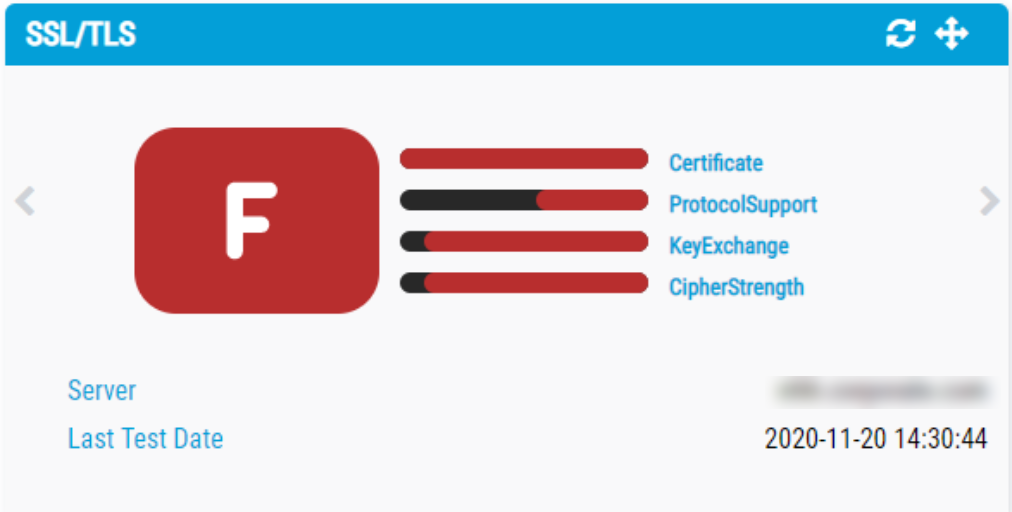
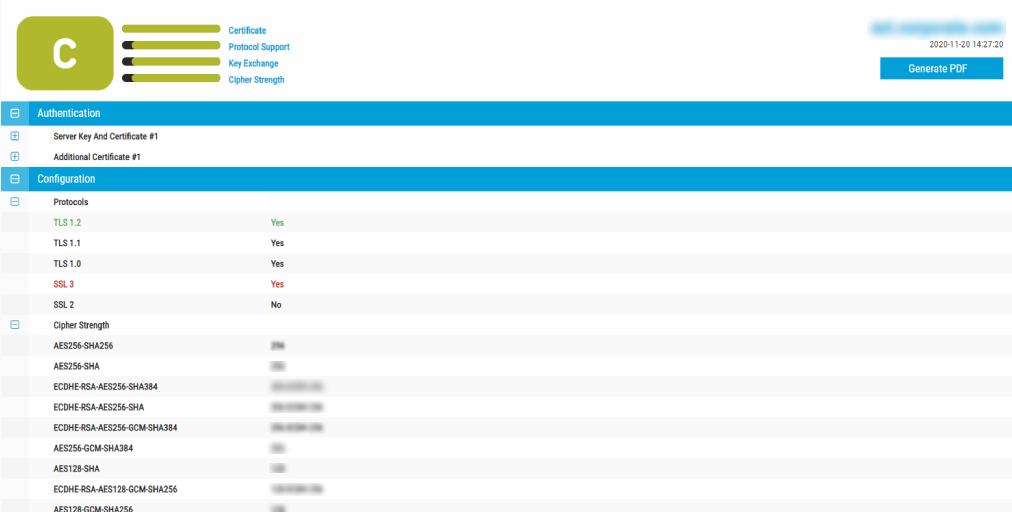
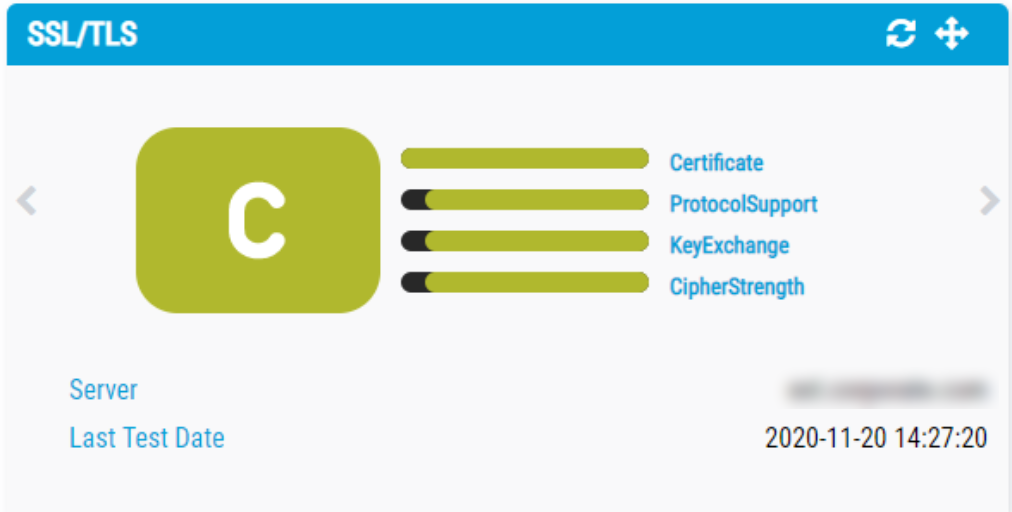
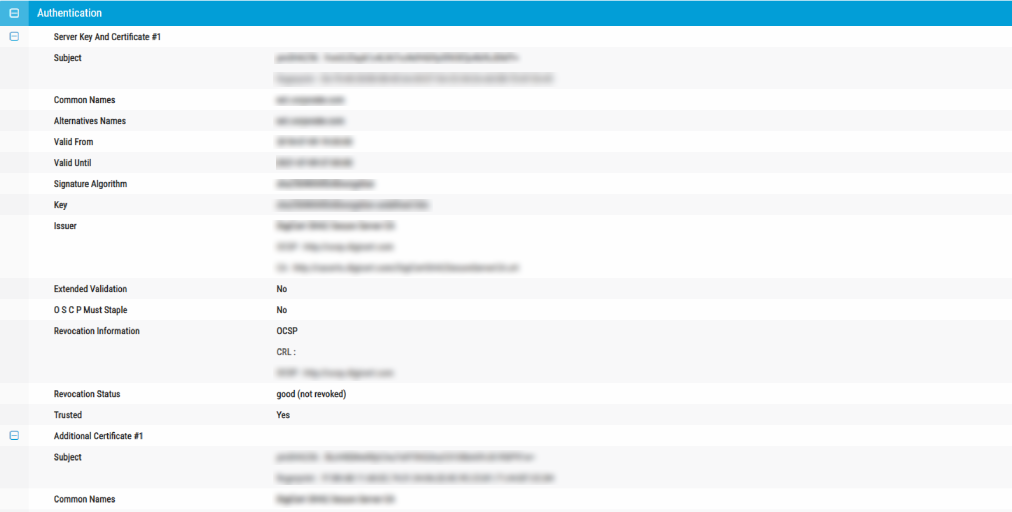
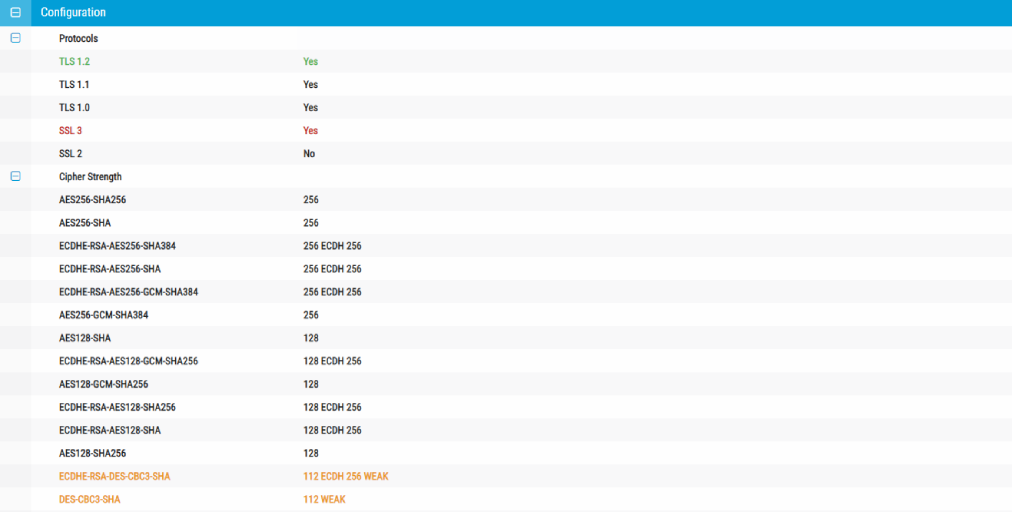
SEGURIDAD DE CERTIFICADOS SSL/TLS
Realice escaneos masivos a toda su infraestructura de TI, en busca de Certificados SSL/TLS e identifique inmediatamente protocolos de cifrado inseguros, certificados próximos a vencer y vulnerabilidades críticas de forma preventiva, antes que los ciberatacantes.

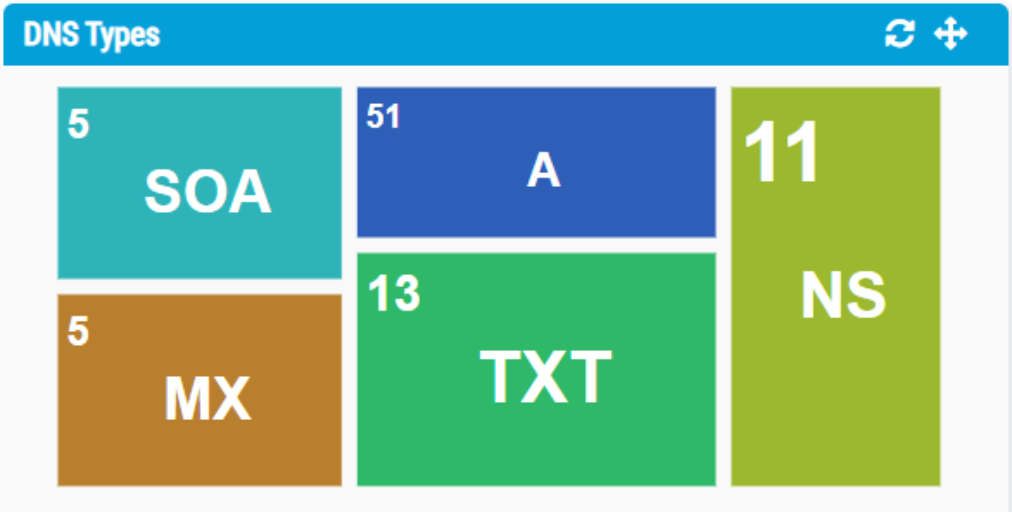
DESCUBRIMIENTO DE SERVICIOS
Tanto en el escaneo de puertos pasivo como el activo, usted podrá contar con un visor que clasifica todos los elementos colectados por tipo de servicio web identificado y si el puerto está abierto, cerrado o filtrado.

Nunca aceptes la forma en que las cosas se han hecho siempre,
como la única forma en que pueden hacerse.
Soporte de nuestro Cyber-SOC
Los escáneres de vulnerabilidades a menudo producen una larga lista de factores de riesgo, y los administradores rara vez pueden resolver todos los riesgos identificados de forma inmediata y efectiva; simplemente requiere demasiados recursos para evaluar y abordar cada elemento.
La licencia de P365 trae una licencia gratuita de Cyber-SOC donde un equipo de profesionales en Seguridad te apoyarán en la remediación de tus riesgos y vulnerabilidades.
Los escáneres de vulnerabilidades a menudo producen una larga lista de factores de riesgo, y los administradores rara vez pueden resolver todos los riesgos identificados de forma inmediata y efectiva; simplemente requiere demasiados recursos para evaluar y abordar cada elemento.
La licencia de P365 trae una licencia gratuita de Cyber-SOC donde un equipo de profesionales en Seguridad te apoyarán en la remediación de tus riesgos y vulnerabilidades.

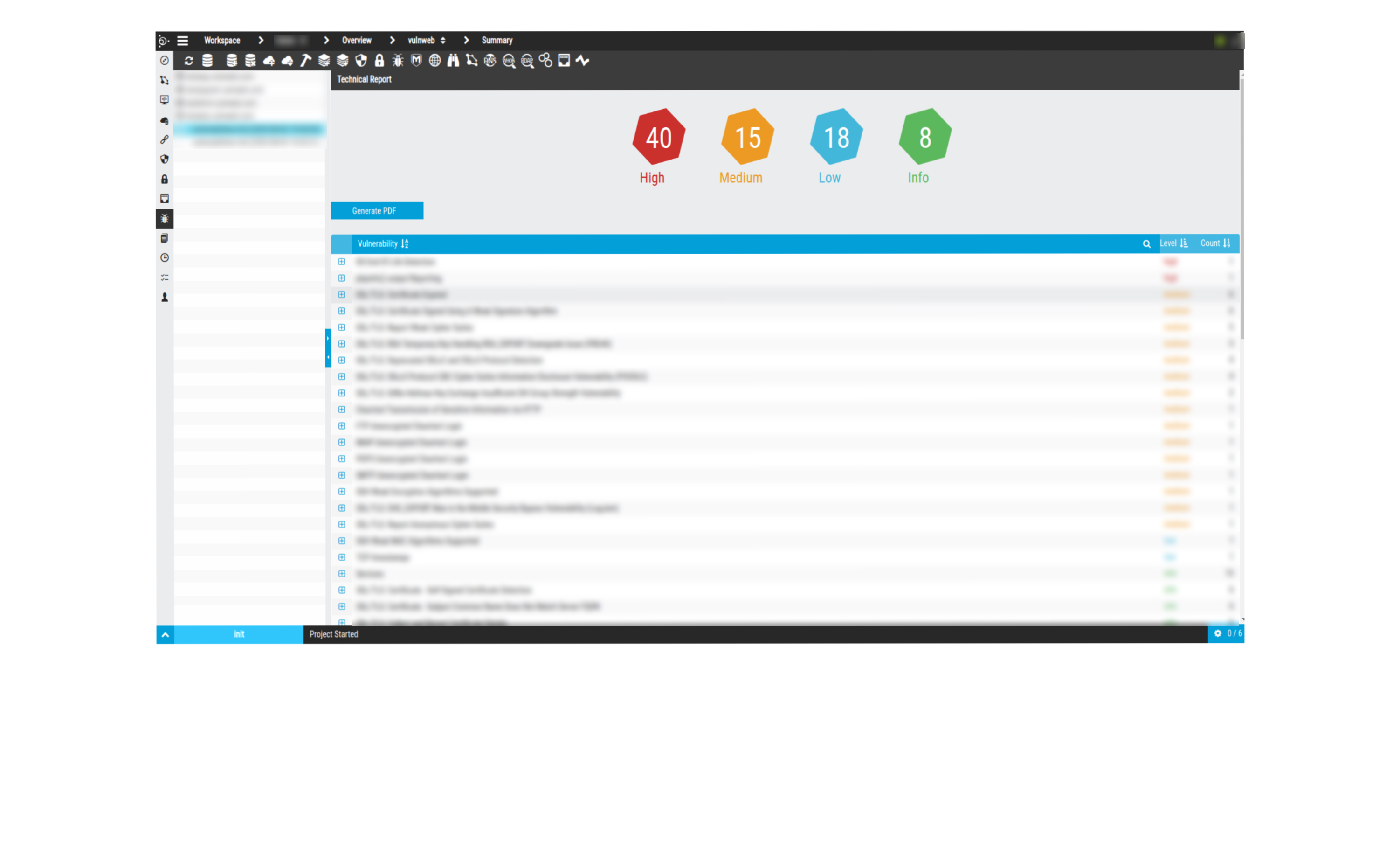
Clasificación y Categorización
No todas las vulnerabilidades son igualmente urgentes. P365 clasifica y categoriza las vulnerabilidades identificadas para ayudar los administradores a priorizar los problemas más preocupantes.
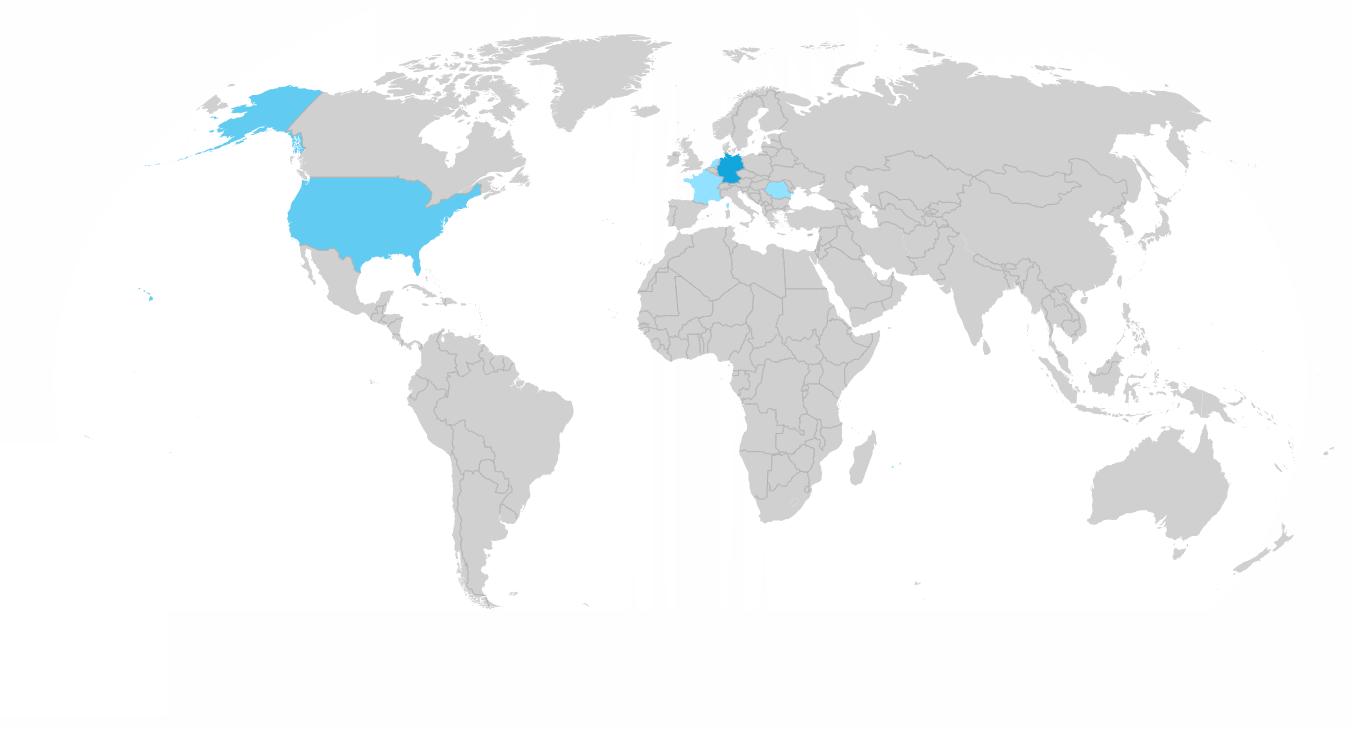
Programa de Canales
Nuestra misión es crear software de ciberseguridad que permita a otras organizaciones evaluar de forma inteligente y persistente su seguridad, riesgos y vulnerabilidades tecnológicas y gracias a nuestro programa de canales podemos llegar cada vez a más y más organizaciones. ¿Estas interesado en nuestro programa de canales? Escríbenos.
CANALES DE DISTRIBUCIÓN
Pentest365 Se distribuye a través de un programa de canales asociados, nuestros socios se enumeran a continuación.